Android 16 平台包含一些可能会影响您的应用的行为变更。以下行为变更将影响在 Android 16 上运行的所有应用,无论采用哪种 targetSdkVersion 都不例外。您应该测试您的应用,然后根据需要酌情修改,以便支持这些变更。
此外,请务必查看仅影响以 Android 16 为目标平台的应用的行为变更列表。
核心功能
Android 16(API 级别 36)包含以下变更,这些变更会修改或扩展 Android 系统的各种核心功能。
JobScheduler 配额优化
Starting in Android 16, we're adjusting regular and expedited job execution runtime quota based on the following factors:
- Which app standby bucket the application is in: in Android 16, active standby buckets will start being enforced by a generous runtime quota.
- If the job starts execution while the app is in a top state: in Android 16, Jobs started while the app is visible to the user and continues after the app becomes invisible, will adhere to the job runtime quota.
- If the job is executing while running a Foreground Service: in Android 16, jobs that are executing while concurrently with a foreground service will adhere to the job runtime quota. If you're leveraging jobs for user initiated data transfer, consider using user initiated data transfer jobs instead.
This change impacts tasks scheduled using WorkManager, JobScheduler, and
DownloadManager. To debug why a job was stopped, we recommend logging why your
job was stopped by calling WorkInfo.getStopReason() (for
JobScheduler jobs, call JobParameters.getStopReason()).
For information about how your app's state affects the resources it can use, see Power management resource limits. For more information on battery-optimal best practices, refer to guidance on optimize battery use for task scheduling APIs.
We also recommend leveraging the new
JobScheduler#getPendingJobReasonsHistory API introduced in
Android 16 to understand why a job has not executed.
Testing
To test your app's behavior, you can enable override of certain job quota optimizations as long as the app is running on an Android 16 device.
To disable enforcement of "top state will adhere to job runtime quota", run the
following adb command:
adb shell am compat enable OVERRIDE_QUOTA_ENFORCEMENT_TO_TOP_STARTED_JOBS APP_PACKAGE_NAME
To disable enforcement of "jobs that are executing while concurrently with a
foreground service will adhere to the job runtime quota", run the following
adb command:
adb shell am compat enable OVERRIDE_QUOTA_ENFORCEMENT_TO_FGS_JOBS APP_PACKAGE_NAME
To test certain app standby bucket behavior, you can set the app standby bucket
of your app using the following adb command:
adb shell am set-standby-bucket APP_PACKAGE_NAME active|working_set|frequent|rare|restricted
To understand the app standby bucket your app is in, you can get the app standby
bucket of your app using the following adb command:
adb shell am get-standby-bucket APP_PACKAGE_NAME
已放弃的空作业停止原因
如果与作业关联的 JobParameters 对象已被垃圾回收,但尚未调用 JobService#jobFinished(JobParameters,
boolean) 来指示作业已完成,则会发生作业被废弃的情况。这表示作业可能会在应用不知情的情况下运行和重新调度。
依赖于 JobScheduler 的应用不会维护对 JobParameters 对象的强引用,并且超时现在将获得新的作业停止原因 STOP_REASON_TIMEOUT_ABANDONED,而不是 STOP_REASON_TIMEOUT。
如果新的作业被废弃停止原因频繁出现,系统会采取缓解措施来降低作业频率。
应用应使用新的停止原因来检测和减少被废弃的作业。
如果您使用的是 WorkManager、AsyncTask 或 DownloadManager,则不会受到影响,因为这些 API 会代表您的应用管理作业生命周期。
完全弃用 JobInfo#setImportantWhileForeground
The JobInfo.Builder#setImportantWhileForeground(boolean)
method indicates the importance of a job while the scheduling app is in the
foreground or when temporarily exempted from background restrictions.
This method has been deprecated since Android 12 (API level 31). Starting in Android 16, it no longer functions effectively and calling this method will be ignored.
This removal of functionality also applies to
JobInfo#isImportantWhileForeground(). Starting in Android
16, if the method is called, the method returns false.
有序广播优先级范围不再是全局
Android 应用可以为广播接收器定义优先级,以控制接收器接收和处理广播的顺序。对于清单声明的接收器,应用可以使用 android:priority 属性来定义优先级;对于上下文注册的接收器,应用可以使用 IntentFilter#setPriority() API 来定义优先级。发送广播时,系统会按接收器的优先级(从高到低)将其传送给接收器。
在 Android 16 中,无法保证使用 android:priority 属性或 IntentFilter#setPriority() 在不同进程中传送广播的顺序。广播优先级仅在同一应用进程内有效,而不会跨所有进程有效。
此外,广播优先级将自动限制在 (SYSTEM_LOW_PRIORITY + 1, SYSTEM_HIGH_PRIORITY - 1) 的范围内。只有系统组件才能将 SYSTEM_LOW_PRIORITY、SYSTEM_HIGH_PRIORITY 设置为广播优先级。
如果您的应用执行以下任一操作,可能会受到影响:
- 您的应用声明了具有相同广播 intent 的多个进程,并且希望根据优先级以特定顺序接收这些 intent。
- 您的应用进程与其他进程交互,并期望以特定顺序接收广播 intent。
如果进程需要相互协调,则应使用其他协调渠道进行通信。
ART 内部变更
Android 16 包含 Android 运行时 (ART) 的最新更新,这些更新可提升 Android 运行时 (ART) 的性能,并支持更多 Java 功能。通过 Google Play 系统更新,搭载 Android 12(API 级别 31)及更高版本的 10 亿多部设备也将受益于这些改进。
发布这些变更后,依赖于 ART 内部结构的库和应用代码在搭载 Android 16 的设备以及通过 Google Play 系统更新来更新 ART 模块的较低 Android 版本上可能无法正常运行。
依赖于内部结构(例如非 SDK 接口)始终会导致兼容性问题,但避免依赖于利用内部 ART 结构的代码(或包含代码的库)尤为重要,因为 ART 更改与设备所运行的平台版本无关,并且会通过 Google Play 系统更新推送到超过 10 亿部设备。
所有开发者都应在 Android 16 上对其应用进行全面测试,以检查其应用是否受到影响。此外,请查看已知问题,了解您的应用是否依赖于我们发现的任何依赖于内部 ART 结构的库。如果您的应用代码或库依赖项受到影响,请尽可能寻找公共 API 替代方案,并在问题跟踪器中创建功能请求,为新用例请求公共 API。
16 KB 页面大小兼容模式
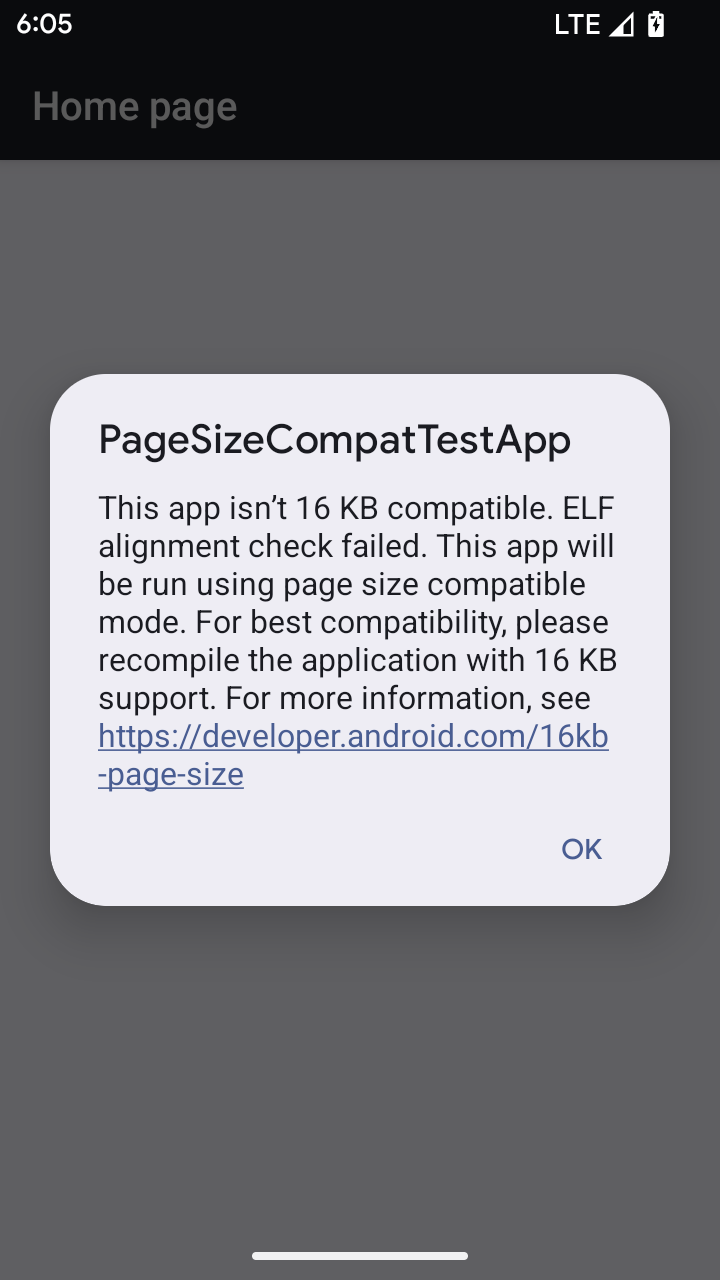
Android 15 引入了对 16 KB 内存页面的支持,以优化平台性能。Android 16 添加了兼容模式,让一些针对 4 KB 内存页面构建的应用可以在配置为 16 KB 内存页面的设备上运行。
当您的应用在搭载 Android 16 或更高版本的设备上运行时,如果 Android 检测到您的应用具有 4 KB 对齐的内存页面,则会自动使用兼容模式并向用户显示通知对话框。在 AndroidManifest.xml 中设置 android:pageSizeCompat 属性以启用向后兼容模式,将会阻止应用启动时显示对话框。如需使用 android:pageSizeCompat 属性,请使用 Android 16 SDK 编译您的应用。
为了实现最佳性能、可靠性和稳定性,应用仍应以 16 KB 对齐。如需了解详情,请参阅我们近期发布的博文,了解如何更新应用以支持 16 KB 的内存页面。
用户体验和系统界面
Android 16(API 级别 36)包含以下变更,旨在打造更一致、更直观的用户体验。
弃用干扰性无障碍功能公告
Android 16 废弃了无障碍功能通告,其特征是使用 announceForAccessibility 或调度 TYPE_ANNOUNCEMENT 无障碍功能事件。这可能会给 TalkBack 和 Android 屏幕阅读器用户带来不一致的用户体验,而替代方案可以更好地满足各种 Android 辅助技术的用户需求。
替代方案示例:
- 对于窗口更改等重大界面更改,请使用
Activity.setTitle(CharSequence)和setAccessibilityPaneTitle(java.lang.CharSequence)。在 Compose 中,使用Modifier.semantics { paneTitle = "paneTitle" } - 如需向用户告知关键界面的更改,请使用
setAccessibilityLiveRegion(int)。在 Compose 中,请使用Modifier.semantics { liveRegion = LiveRegionMode.[Polite|Assertive]}。应谨慎使用这些事件,因为它们可能会在每次更新视图时生成通知。 - 如需向用户发送错误通知,请发送类型为
AccessibilityEvent#CONTENT_CHANGE_TYPE_ERROR的AccessibilityEvent并设置AccessibilityNodeInfo#setError(CharSequence),或使用TextView#setError(CharSequence)。
已废弃的 announceForAccessibility API 的参考文档中包含有关建议替代方案的更多详细信息。
支持“三按钮”导航
Android 16 brings predictive back support to the 3-button navigation for apps that have properly migrated to predictive back. Long-pressing the back button initiates a predictive back animation, giving you a preview of where the back swipe takes you.
This behavior applies across all areas of the system that support predictive back animations, including the system animations (back-to-home, cross-task, and cross-activity).
设备规格
Android 16(API 级别 36)在虚拟设备所有者将应用投影到显示屏时,对应用做出了以下更改。
虚拟设备所有者替换
A virtual device owner is a trusted or privileged app that creates and manages a virtual device. Virtual device owners run apps on a virtual device and then project the apps to the display of a remote device, such as a personal computer, virtual reality device, or car infotainment system. The virtual device owner is on a local device, such as a mobile phone.
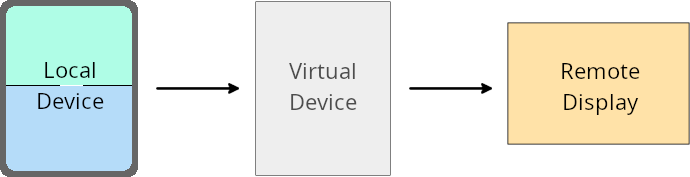
Per-app overrides
On devices running Android 16 (API level 36), virtual device owners can override app settings on select virtual devices that the virtual device owners manage. For example, to improve app layout, a virtual device owner can ignore orientation, aspect ratio, and resizability restrictions when projecting apps onto an external display.
Common breaking changes
The Android 16 behavior might impact your app's UI on large screen form factors such as car displays or Chromebooks, especially layouts that were designed for small displays in portrait orientation. To learn how to make your app adaptive for all device form factors, see About adaptive layouts.
References
安全
Android 16(API 级别 36)包含多项变更,旨在提升系统安全性,帮助保护应用和用户免受恶意应用的侵害。
安全性更强,可防范 Intent 重定向攻击
Android 16 provides default security against general Intent redirection
attacks, with minimum compatibility and developer changes required.
We are introducing by-default security hardening solutions to Intent
redirection exploits. In most cases, apps that use intents normally won't
experience any compatibility issues; we've gathered metrics throughout our
development process to monitor which apps might experience breakages.
Intent redirection in Android occurs when an attacker can partly or fully control the contents of an intent used to launch a new component in the context of a vulnerable app, while the victim app launches an untrusted sub-level intent in an extras field of an ("top-level") Intent. This can lead to the attacker app launching private components in the context of the victim app, triggering privileged actions, or gaining URI access to sensitive data, potentially leading to data theft and arbitrary code execution.
Opt out of Intent redirection handling
Android 16 introduces a new API that allows apps to opt out of launch security protections. This might be necessary in specific cases where the default security behavior interferes with legitimate app use cases.
For applications compiling against Android 16 (API level 36) SDK or higher
You can directly use the removeLaunchSecurityProtection() method on the Intent
object.
val i = intent
val iSublevel: Intent? = i.getParcelableExtra("sub_intent")
iSublevel?.removeLaunchSecurityProtection() // Opt out from hardening
iSublevel?.let { startActivity(it) }
For applications compiling against Android 15 (API level 35) or lower
While not recommended, you can use reflection to access the
removeLaunchSecurityProtection() method.
val i = intent
val iSublevel: Intent? = i.getParcelableExtra("sub_intent", Intent::class.java)
try {
val removeLaunchSecurityProtection = Intent::class.java.getDeclaredMethod("removeLaunchSecurityProtection")
removeLaunchSecurityProtection.invoke(iSublevel)
} catch (e: Exception) {
// Handle the exception, e.g., log it
} // Opt-out from the security hardening using reflection
iSublevel?.let { startActivity(it) }
不再向配套应用通知发现超时
Android 16 在配套设备配对流程期间引入了一种新行为,以防恶意应用侵犯用户的位置信息隐私。在 Android 16 上运行的所有配套应用都不再直接通过 RESULT_DISCOVERY_TIMEOUT 收到发现超时通知。而是通过可视对话框通知用户超时事件。当用户关闭对话框时,系统会通过 RESULT_USER_REJECTED 提醒应用关联失败。
搜索时长也从原来的 20 秒延长到了 30 秒,并且用户可以在搜索期间的任何时间停止设备发现。如果在开始搜索的前 20 秒内发现了至少 1 部设备,CDM 会停止搜索其他设备。
连接
Android 16(API 级别 36)在蓝牙堆栈中进行了以下更改,以改善与外围设备的连接。
改进了债券丢失处理
Starting in Android 16, the Bluetooth stack has been updated to improve security and user experience when a remote bond loss is detected. Previously, the system would automatically remove the bond and initiate a new pairing process, which could lead to unintentional re-pairing. We have seen in many instances apps not taking care of the bond loss event in a consistent way.
To unify the experience, Android 16 improved the bond loss handling to the system. If a previously bonded Bluetooth device could not be authenticated upon reconnection, the system will disconnect the link, retain local bond information, and display a system dialog informing users of the bond loss and directing them to re-pair.

